StrandHogg 2.0 Steals Data From Real Apps
Named after the Norse term for an ancient Viking technique for coastal raids, StrandHogg 2.0 is a nefarious new update to an earlier trojan-like malware.
Named after the Norse term for an ancient Viking technique for coastal raids, StrandHogg 2.0 is a nefarious new update to an earlier trojan-like malware. Its particular way of working undercover and seizing user data is notable. The relentless inventiveness of hackers is very much on display with this latest threat.
Strandhogg 2.0: Worse Than The Original
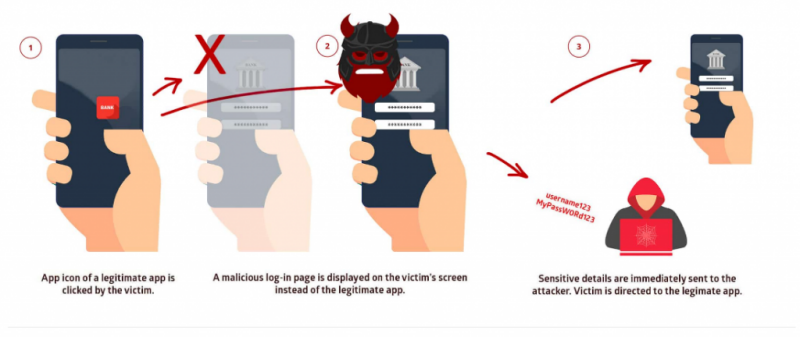
“StrandHogg 1.0” used Android’s task affinity to hijack applications—by matching the packageName of any other app, then allowing “TaskReparenting,” the StrandHogg app would be launched, undercover, in place of the target app — then share the information with the attacker and the targeted app (to go unnoticed).
Image Source: Promon
Emilio Simoni, research director at dfndr lab explains: “Using this method, you would see (for one typical example) what looks like a fully legitimate Gmail icon on your phone, with the usual login dialogue — just exactly as it would appear when you’re logging back into your account. But once you enter your credentials, you’ve unknowingly shared them with the attacker too. To shield its intervention, your info is also sent to Gmail (or whatever other legitimate application has been hijacked), continuing your transaction and leaving no signs you’ve been compromised. The malware comes on board in the form of innocent looking game apps — one named SuperHappyFunGame — but it does its worst work undercover.”
StrandHogg’s 1.0 weakness was the presence of sketchy task affinity codes in the Android Manifest. Scouring for the 1.0 version required simply scanning the Google Play store for these problematic taskAffinity declarations. But StrandHogg 2.0 doesn’t require any special settings, because the attacking code isn’t necessarily present on the Play Store. Instead, the attacker just downloads the attack code later, once the trojan app or game has taken up residence.
StrandHogg 2.0 also hijacks additional data via app permissions: so contacts, photos, and it can even victim’s movements and location are compromised. Simoni advises: “With the right permissions, StrandHogg 2.0 can even siphon off entire text message conversations, which can enable hackers to defeat two-factor authentication protections.”
The Norwegian security firm Promon, the firm that gave the malware its name, suggests that updating Android devices with the latest security updates — out now — will fix the vulnerability. Users are advised to update their Android devices as soon as possible.
“However,” Simoni warns, “the key is protecting yourself from the next StrandHogg. For that, you need a front line of defense.”
Protecting Your Devices and Data From Unsafe Apps
You should always count on a extra layer of security for your phone. dfndr security, for example, has a Safe App Installer feature that can operate as your advance-line of defense against apps like SuperHappyFunGame, and the next generation of trojans StrandHogg uses. Safe App Installer will also keep you protected from all other malicious apps. “The feature lets you know if an app is unsafe before you even install it,” Simoni advises, “and our team does the work to constantly update our database of malicious apps.” With Safe App Installer, every app you consult before installation will be rated for trust.
There are two levels of alert if Safe App Installer discovers an issue:
- Security Alert: If the app is malware.
- Privacy Alert: If the app already experienced a data breach
An app is rated as Trusted only if the app is not malware or has never experienced a data breach.
dfndr security also offers Anti-Theft Protection for your device, and Identity theft protection for you. “Our PRO package has been very thoroughly thought out to provide users with the full suite of protections they need,” Simoni concludes.
We’ll continue to provide updates here on the PSafe blog for new malware that could compromise your security and safety — stay tuned!